ReasonPS Source Leak – What Happened & How RSPS Owners Can Protect Themselves
The ReasonPS community has recently been shaken by reports that its source code has been leaked. The project, known for its rapid growth and strong player retention, was reportedly built on a base derived from the Runite/Kronos ecosystem — a widely used foundation in the RSPS scene.
This incident highlights a recurring issue within the private server space: security, trust, and developer risk.
📌 What is ReasonPS?
ReasonPS positioned itself as a community-driven OSRS experience, aiming to improve on the grind-heavy nature of Old School RuneScape.
Key highlights included:
-
500+ real concurrent players during peak times
-
Custom end-game systems like Royal Titans and Echo Bosses (Raids 4)
-
Fully integrated RuneLite client with HD plugins
-
Continuous updates (50+ logs within 6 months)
-
Custom bosses like Yama, Huey, and DT2 content
The server marketed itself as a long-term, grind-friendly alternative with meaningful progression.
⚠️ The Source Leak – What We Know
While full technical details are still emerging, internal discussions suggest:
-
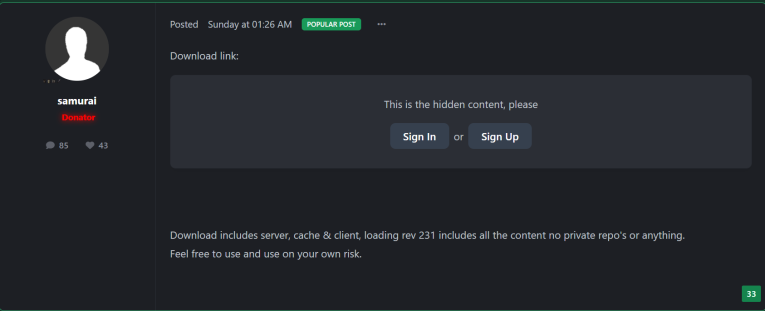
The source was based on a Runite/Kronos framework
-
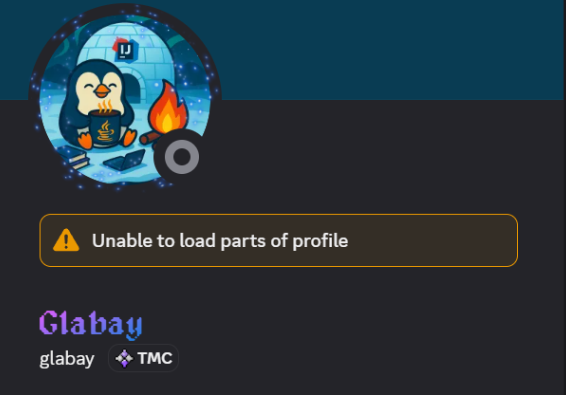
The leak may have originated from a developer identified as “Glabay,” whose Discord handle has been referenced in community discussions.
-
The breach appears to be internal, rather than a direct external exploit
-
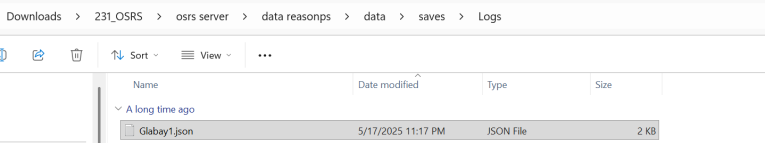
A save file in the logs data folder(this is for localhost use only) has the most recent user Glabay1.json
-
Log files, Gradle build files, and other digital artifacts may contain information that could be used to trace activity back to Glabay.
This is a common pattern in RSPS leaks — trusted access turning into the biggest vulnerability.
🔍 Why This Matters for the RSPS Scene
Source leaks don’t just affect one server — they ripple across the entire ecosystem:
-
Clones appear quickly, damaging originality
-
Economies collapse if dupes or exploits are exposed
-
Player trust drops, especially for high-donation communities
-
Competitors gain unfair advantages
In a space where many servers rely on similar bases, one leak can expose vulnerabilities across multiple projects.
🛡️ How RSPS Owners Can Prevent This
We’ve previously covered server security in detail here:
👉 https://rspstoplist.com/blogs/25-secured-windows-rdp-environment-for-rsps/
Here’s a simplified breakdown every RSPS owner should follow:
1. Vet Your Developers Thoroughly
-
Always research past work and reputation
-
Avoid giving full access immediately
-
Use staged permissions (dev → senior → core)
2. Lock Down Your Infrastructure
-
Use secured VPS environments (preferably anti-leak / “leech-proof”)
-
Restrict RDP access by IP
-
Disable unnecessary services
3. Separate Your Systems
-
Keep game server, webstore, and database isolated
-
Never store full source + credentials in the same place
4. Monitor Everything
-
Log file access and downloads
-
Track unusual behavior (large transfers, off-hour access)
-
Use alerts for suspicious activity
5. Use Version Control Properly
-
Private repositories only (GitHub/GitLab self-hosted preferred)
-
Limit cloning permissions
-
Audit commits regularly
🧠 The Reality of RSPS Development
The biggest takeaway from the ReasonPS situation:
Your biggest risk is not hackers — it’s the people you trust.
Most major leaks in RSPS history come from:
-
Disgruntled developers
-
Internal disputes
-
Poor access control
Not sophisticated cyber attacks.
.gif.624b6b02e8356506d3900a34cdc38500.gif)

0 Comments
Recommended Comments
There are no comments to display.
Please sign in to comment
You will be able to leave a comment after signing in
Sign In Now